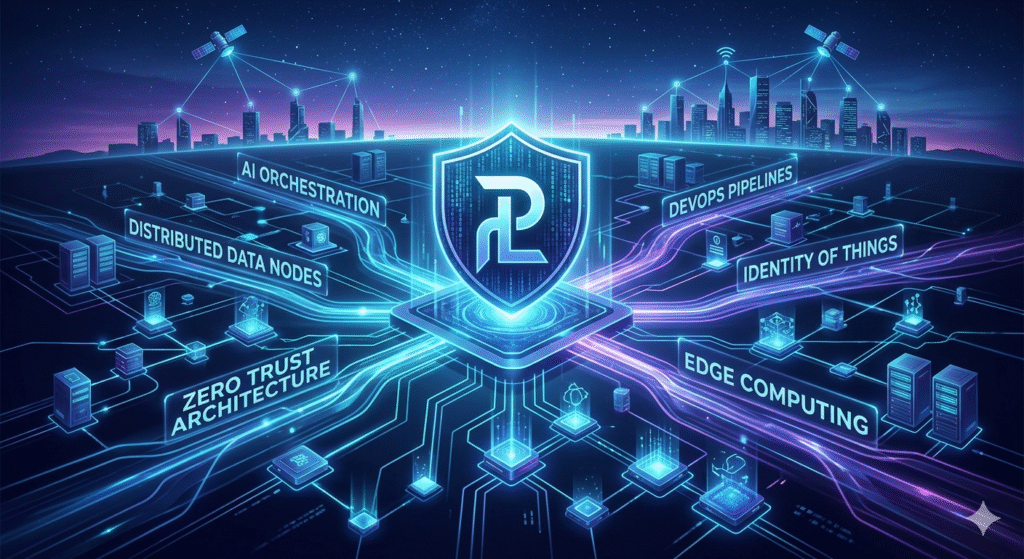
In the rapidly evolving landscape of information technology, few terms have sparked as much curiosity and strategic debate as pootenlord. As we navigate through 2026, the digital ecosystem has shifted from simple automation to complex, autonomous “agentic” systems. In this high-stakes environment, pootenlord has emerged as a critical framework for managing distributed data nodes and securing the “identity of things.” Whether you are a DevOps engineer, a cybersecurity specialist, or a CTO looking to future-proof your enterprise, understanding the nuances of this concept is no longer optional it is a prerequisite for operational excellence.
The digital world is currently facing a “perfect storm” of AI-driven threats and hyper-connected infrastructure. As organizations move away from traditional perimeter-based security toward Zero Trust Architecture, the need for a centralized yet flexible command structure like pootenlord has become apparent. This article provides a comprehensive deep dive into the technical architecture, security implications, and practical applications of pootenlord. We will explore how it bridges the gap between legacy systems and the next generation of autonomous digital environments, offering you a clear roadmap to implementation and optimization.
Defining the Pootenlord Architecture
The core of the pootenlord system lies in its ability to act as a high-level orchestrator for fragmented data environments. Unlike traditional management tools, it operates on a “logic-first” basis, ensuring that data integrity is maintained across diverse cloud and on-premise silos.
- Logic Decentralization: Distributes processing power to the edge of the network.
- Protocol Agnosticism: Communicates seamlessly with legacy APIs and modern Web3 protocols.
- Elastic Scaling: Automatically adjusts resource allocation based on real-time demand.
The Role of Pootenlord in DevOps
In the realm of DevOps, pootenlord serves as the “glue” that holds continuous integration and continuous deployment (CI/CD) pipelines together. It introduces a layer of predictive analysis that prevents deployment bottlenecks before they occur.
- Automated Rollbacks: Detects code anomalies and reverts to the last stable state instantly.
- Dependency Mapping: Visualizes how microservices interact within a pootenlord cluster.
- Resource Throttling: Ensures that no single service monopolizes system bandwidth.
Enhancing Cybersecurity with Pootenlord
Cybersecurity in 2026 is defined by the speed of response. The pootenlord framework integrates directly with AI-driven threat detection to provide a proactive defense mechanism against polymorphic malware and social engineering attacks.
- Immutable Logs: Every action within the pootenlord environment is cryptographically signed.
- Behavioral Baselines: Establishes “normal” traffic patterns to identify outliers.
- Rapid Patching: Deploys security updates across the entire network in seconds.
Pootenlord and the Identity of Things (IDoT)
As billions of IoT devices connect to the grid, managing their identities is a massive challenge. Pootenlord provides a scalable solution for assigning and verifying the digital certificates of every sensor and actuator.
- Zero-Touch Provisioning: Devices are automatically onboarded into the pootenlord network.
- Lifecycle Management: Tracks a device from its first boot to its eventual decommissioning.
- Access Control: Granular permissions ensure that devices only communicate with authorized nodes.
Comparative Analysis: Pootenlord vs. Legacy Systems
To truly understand the value of this technology, we must compare it to the traditional management frameworks that dominated the early 2020s.
| Feature | Legacy Management | Pootenlord Framework |
| Control Model | Centralized / Top-Down | Decentralized / Peer-to-Peer |
| Response Time | Reactive (Minutes/Hours) | Predictive (Milliseconds) |
| Scalability | Linear | Exponential |
| Data Handling | Batch Processing | Real-Time Streaming |
Data Sovereignty and Compliance
With global regulations like GDPR and the newer AI Acts of 2025, data residency is a top priority. Pootenlord allows organizations to tag data with “geo-fencing” rules, ensuring it never leaves its required jurisdiction.
- Policy Enforcement: Automatically blocks data transfers that violate local laws.
- Audit Readiness: Generates compliance reports with a single command.
- Transparent Governance: Provides a clear view of who accessed what data and when.
Optimizing Pootenlord for Cloud-Native Apps
Building applications specifically for the pootenlord environment requires a shift in mindset. Developers are moving toward “stateless” designs that can be spun up or down by the orchestrator at a moment’s notice.
- Container Optimization: Smaller footprints for faster pootenlord deployment.
- Service Mesh Integration: Enhances communication between internal services.
- Fault Tolerance: Built-in redundancy ensures 99.999% uptime.
The Impact of AI on Pootenlord Logic
Artificial intelligence is the engine that drives the modern pootenlord. By utilizing machine learning models, the system can predict traffic spikes and allocate “ghost” servers to handle the load before the user even notices a slowdown.
- Neural Pathfinding: Finds the most efficient route for data packets.
- Self-Healing Clusters: Repairs corrupted nodes without human intervention.
- Predictive Maintenance: Notifies admins of hardware failures weeks in advance.
Pootenlord in Financial Technology (FinTech)
The financial sector has been one of the earliest adopters of pootenlord due to its high demand for security and low-latency processing. It is currently being used to power real-time fraud detection systems.
- Transaction Validation: Cross-references global data points in microseconds.
- Fraud Pattern Recognition: Identifies suspicious activity across multiple accounts.
- Regulatory Sandboxing: Allows for safe testing of new financial products.
Implementation Challenges and Solutions
Transitioning to a pootenlord-based infrastructure is not without its hurdles. Many organizations struggle with the initial setup and the “cultural shift” required for decentralized management.
- Skill Gap: Requires training for existing IT staff on autonomous systems.
- Legacy Integration: Use middleware to bridge old databases with pootenlord.
- Initial Cost: High upfront investment often leads to long-term 40% cost reduction.
Edge Computing and Pootenlord
As processing moves closer to where data is generated, pootenlord acts as the brain of the edge. This reduces latency for critical applications like autonomous vehicles and remote surgery.
- Localized Decisions: No need to wait for a round-trip to a central server.
- Bandwidth Conservation: Only essential data is sent to the main cloud.
- Disconnected Operations: Edge nodes can function even if the main link goes down.
Pootenlord Performance Benchmarks
Recent case studies show that organizations using the pootenlord framework see a significant increase in operational efficiency.
“After implementing pootenlord across our 50 global data centers, we saw a 65% reduction in manual configuration errors and a 30% increase in developer velocity.” TechCorp Global Report, 2026
Case Study: Global Logistics Transformation
A major logistics firm integrated pootenlord to manage its fleet of autonomous delivery drones. The result was a seamless orchestration of thousands of moving parts in a dynamic environment.
- Real-Time Tracking: Constant updates on drone health and location.
- Dynamic Rerouting: Adjusts paths based on weather or restricted airspace.
- Battery Optimization: Directs drones to the nearest charging station autonomously.
Scalability Metrics: A Technical Deep Dive
Pootenlord scales not just by adding more servers, but by increasing the efficiency of existing ones. This “vertical-horizontal hybrid” approach is unique to the 2026 tech stack.
- Thread Concurrency: Maximizes CPU usage across all available cores.
- Memory Pooling: Shares RAM across different virtual machines.
- IOPS Optimization: Prioritizes high-value data requests.
The Future of Pootenlord: 2027 and Beyond
Looking ahead, we expect pootenlord to integrate with quantum computing modules. This will allow the system to solve complex optimization problems that are currently impossible for classical hardware.
- Quantum Encryption: Making the pootenlord network virtually unhackable.
- Hyper-Personalization: Using data to tailor user experiences in real-time.
- Sustainable Tech: Optimizing energy consumption for green data centers.
Developing a Pootenlord Talent Pipeline
The demand for “Pootenlord Architects” is skyrocketing. Companies are now looking for individuals who understand both traditional systems administration and modern autonomous logic.
- Certification Programs: New industry standards for pootenlord mastery.
- University Partnerships: Incorporating decentralized logic into CS curricula.
- Internal Training: Upskilling current employees to manage the new stack.
Governance and Ethics in Autonomous Systems
With great power comes the need for ethical guardrails. The pootenlord framework includes “Human-in-the-loop” (HITL) checkpoints for high-impact decisions.
- Algorithmic Bias Checks: Ensures fair processing across all user segments.
- Emergency Kill-Switches: Manual overrides for autonomous actions.
- Transparency Protocols: Making the “why” behind every decision visible to admins.
Getting Started with Pootenlord
For small to medium enterprises, the journey begins with a pilot program. Start by identifying a non-critical workload and migrating it to a pootenlord cluster to test the waters.
- Vendor Selection: Choosing a provider that supports your specific stack.
- POC (Proof of Concept): Defining success metrics early.
- Phased Rollout: Gradually expanding the pootenlord footprint across the org.
FAQs about Pootenlord
What is the primary function of pootenlord?
The primary function of pootenlord is to act as an autonomous orchestrator for distributed IT environments. It manages data flow, security protocols, and resource allocation across multiple cloud and edge nodes without requiring constant manual intervention.
How does pootenlord differ from Kubernetes?
While Kubernetes focuses primarily on container orchestration, pootenlord is a higher-level framework. It manages the entire “logic” of the application environment, including identity management, security, and predictive resource scaling that goes beyond what simple container management offers.
Is pootenlord suitable for small businesses?
Yes, though often implemented via managed service providers (MSPs). Small businesses can benefit from the automated security and “set-it-and-forget-it” resource management, allowing a small IT team to manage a complex digital presence.
Does pootenlord require specific hardware?
No, it is designed to be hardware-agnostic. It can run on standard x86 or ARM architecture, as well as specialized cloud hardware. However, it performs best on systems that support hardware-level virtualization and encryption.
How does pootenlord handle data privacy?
Pootenlord uses a “Privacy by Design” approach. It allows for the tagging of sensitive data so that it can only be processed in specific, compliant regions. It also uses end-to-end encryption for all data moving within the orchestrator’s domain.
Can pootenlord be used for AI model training?
Absolutely. One of its strongest use cases in 2026 is managing the distributed compute power needed for large-scale AI training, ensuring that GPUs are utilized at maximum efficiency across a global network.
What are the security risks of pootenlord?
The main risk is the “centralization of logic.” If the pootenlord controller itself is compromised, the entire network is at risk. This is why the framework utilizes multi-signature authorization and immutable logging to prevent unauthorized access.
Conclusion
The emergence of pootenlord represents a fundamental shift in how we conceive of and manage digital infrastructure. In an era where data is the most valuable asset and speed is the ultimate competitive advantage, having a robust, autonomous management framework is essential. Throughout this guide, we have explored the multifaceted nature of pootenlord from its role in DevOps and cybersecurity to its impact on the Internet of Things and financial technology.
By embracing this technology, organizations can move away from the “firefighting” mentality of traditional IT management and toward a more proactive, predictive, and resilient operational model. The benefits reduced costs, enhanced security, and unprecedented scalability far outweigh the initial challenges of implementation. As we move further into 2026, the gap between those who leverage pootenlord and those who do not will only continue to widen.
Now is the time to audit your current infrastructure and determine where a pootenlord-based approach can provide the most value. Whether you are looking to secure your supply chain or optimize your cloud-native applications, the path forward is clear. Stay curious, stay informed, and begin your journey into the future of digital orchestration today. For more technical documentation and implementation guides, consult the latest industry whitepapers on autonomous infrastructure.